Digital Forensics in Cybercrime Investigations — Comprehensive Guide
Digital forensics is the science and practice of collecting, preserving, analyzing, and presenting digital evidence in a legally admissible manner. It’s critical for law enforcement, corporate investigations, and cybersecurity incidents. Analysts deal with computers, mobile devices, emails, social media, and networks to uncover cybercrime evidence. Advanced tools like FTK, EnCase, Autopsy, XRY, and others allow structured, defensible investigations.
What is digital forensics?
Digital forensics, also called computer forensics, is a branch of forensic science focused on recovering and investigating material found in digital devices. Unlike standard IT troubleshooting, digital forensics aims to uncover evidence that can be used in court or internal investigations, maintaining the integrity of data throughout the process.
Key aspects:
Acquisition: Securely copying data without altering the original.
Preservation: Maintaining the chain of custody for legal purposes.
Analysis: Extracting meaningful evidence — deleted files, logs, communication records.
Presentation: Summarizing findings in reports or expert testimony.
Digital forensics applies to computers, smartphones, servers, cloud environments, IoT devices, and networks.
How digital forensics supports law enforcement
Law enforcement uses digital forensics to:
-
Investigate cybercrime: Identify attackers, trace fraud, hacking, ransomware, phishing, and malware incidents.
-
Recover deleted or hidden data: Many cybercriminals attempt to erase traces of wrongdoing; forensic methods can recover deleted files, logs, and metadata.
-
Establish timelines: By analyzing timestamps and logs, investigators can determine when actions occurred and reconstruct events.
-
Link digital evidence to suspects: IP logs, device IDs, email headers, and metadata help tie digital actions to real-world identities.
-
Support prosecutions: Forensic reports are designed to hold up in court, providing clear, reproducible evidence.
Example: In ransomware attacks, digital forensics can trace the initial compromise, the malware’s behavior, and even the flow of cryptocurrency ransom payments.
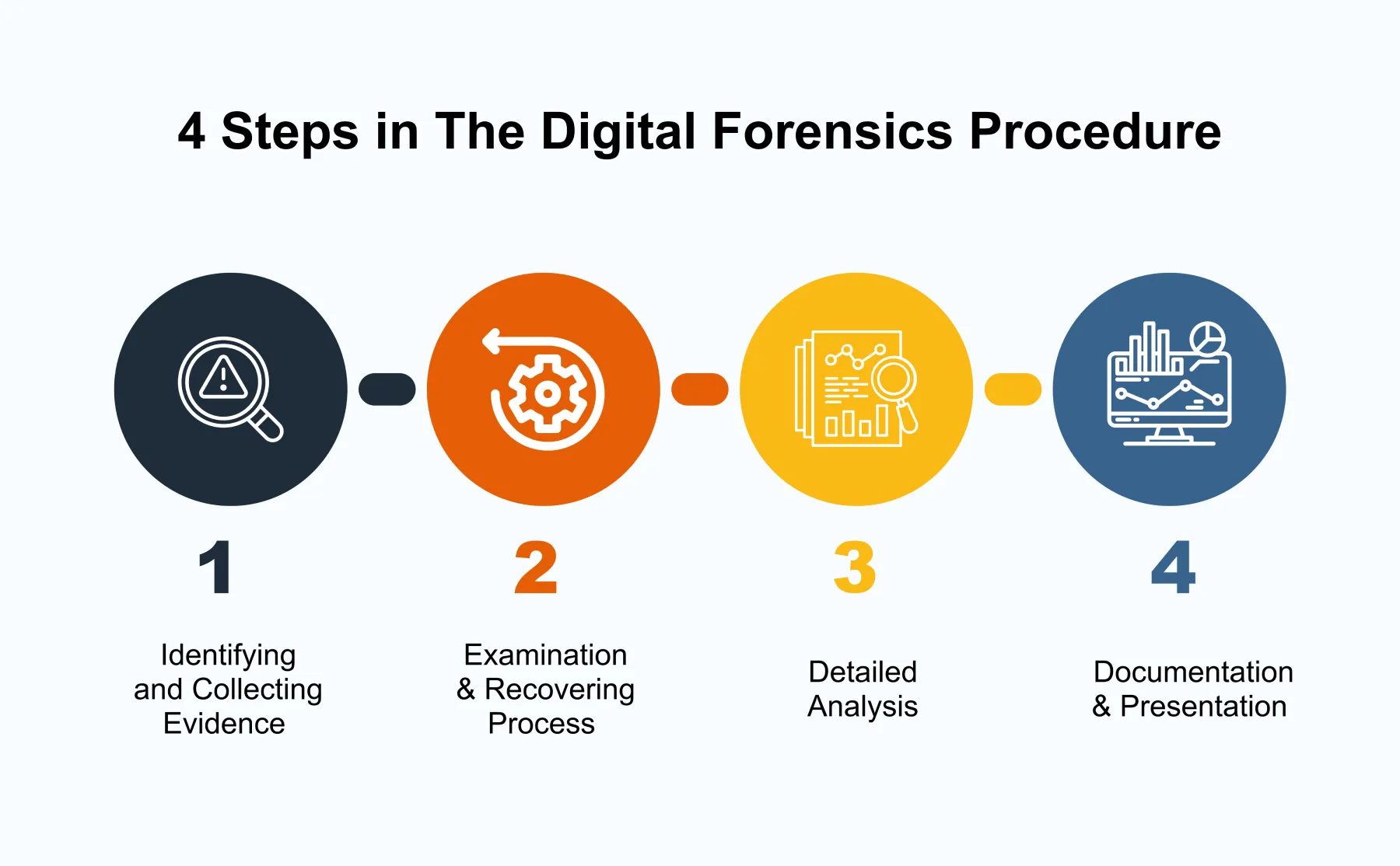
Steps in a digital forensic investigation
-
Preparation: Define scope, select tools, ensure proper legal permissions.
-
Acquisition: Create bit-for-bit copies (images) of devices or storage.
-
Preservation: Secure evidence with hashes (MD5/SHA256) and maintain chain of custody.
-
Examination & Analysis: Identify relevant files, emails, logs, deleted data, and reconstruct events.
-
Documentation: Detailed notes, screenshots, and chain-of-custody logs.
-
Reporting: Generate a legal, court-ready report summarizing findings and methods used.